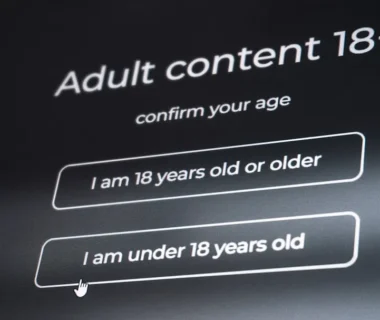
CVE-2025-60710: CISA’s active‑exploit designation turns a TaskHost privilege bug into a two‑week patch emergency
CISA’s addition of CVE-2025-60710 to the Known Exploited Vulnerabilities list makes a previously theoretical Windows Task Host privilege escalation a present operational threat: federal agencies have two weeks under BOD 22‑01 to patch, and all organizations should treat this as a priority where detection will not substitute for patching. CISA’s designation versus the bug’s mechanics […]